Description
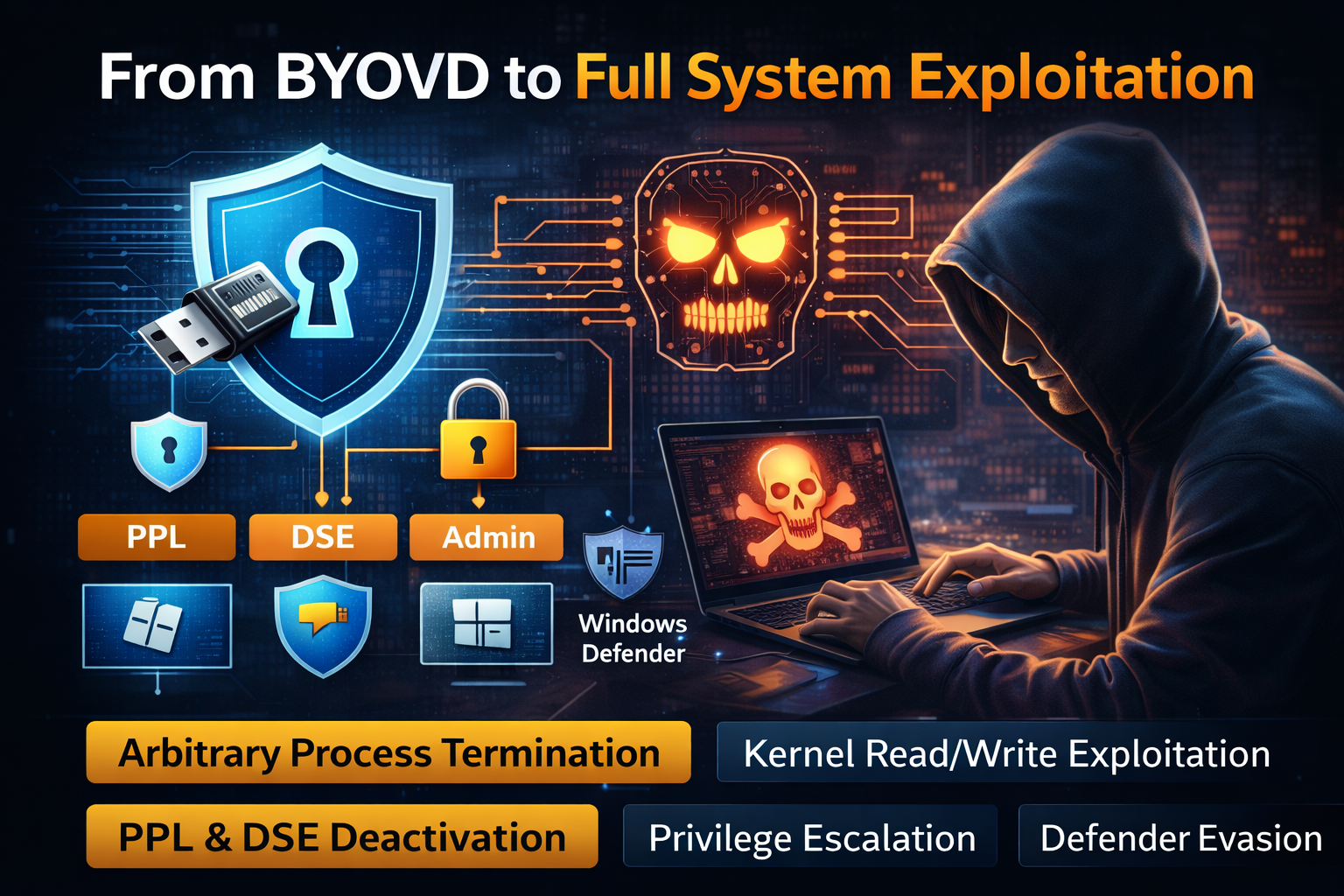
This module covers the transition from kernel read/write primitives to complete system exploitation on Windows. Starting from a single vulnerable driver loaded via BYOVD, six techniques are built on top of the same primitive: arbitrary process termination, PPL deactivation, Driver Signature Enforcement bypass, local privilege escalation to SYSTEM, persistent AV evasion through restart loops, and DKOM-based process hiding. Each technique targets a different kernel data structure EPROCESS, g_CiOptions, ActiveProcessLinks — demonstrating how much control a single write primitive unlocks. The module closes by examining why HVCI and the vulnerable driver blocklist are the only defensive controls that address the root cause rather than individual symptoms.



There are no reviews yet.