
Malware Development Text Modules
Learn the best malware techniques for Windows OS, with content ranging from beginner to advanced levels. All implementations are developed in C++.
Gain access to a new malware development module every 15 days. And of course, all the previous ones. Each module offers over 45 minutes of reading time. Available from $5/month, $12.99/3 months, or $49.99/year. Alternatively, you can purchase individual modules for $1.99 each.
You can also get lifetime access to all the modules for a one-time payment of $100.
*We accept PayPal, Credit Card and Cryptocurrency, for this last option send a email to s12deff@gmail.com*
1 Month Subscription
Monthly Payment

$5/Month
3 Months Subscription
Quarterly Payment

$12.99/3 Months
1 Year Subscription
Annual Payment

$49.99/Year
Lifetime Access
Unique Payment
$100
Subscription Plans Available
One-time purchases ($1.99) are limited to single modules. For full access to all modules, including new and previous content, consider our subscription, or lifetime plans.
| Module | Category | Duration | Pages | Date | Actions |
|---|---|---|---|---|---|

Process Injection Part III
This module explores advanced process injection techniques, expanding beyond classic shellcode injection into DLL and executable-based methods. It also introduces a new approach to generating custom shellcode using modern C++ techniques.
|
Injection | 41 min. | 45 | 20/04/2026 | |
From BYOVD to Full System Exploitation
From vulnerable driver primitives to full system control: PPL bypass, DSE disable, token theft, and kernel full control.
|
Kernel | 30 min. | 38 | 05/04/2026 | |
AV & EDR Hooking Evasion Part 1
Learn how AV and EDR products hook Windows API calls and six practical techniques to bypass them entirely from userland.
|
Evasion | 37 min. | 34 | 22/03/2026 | |
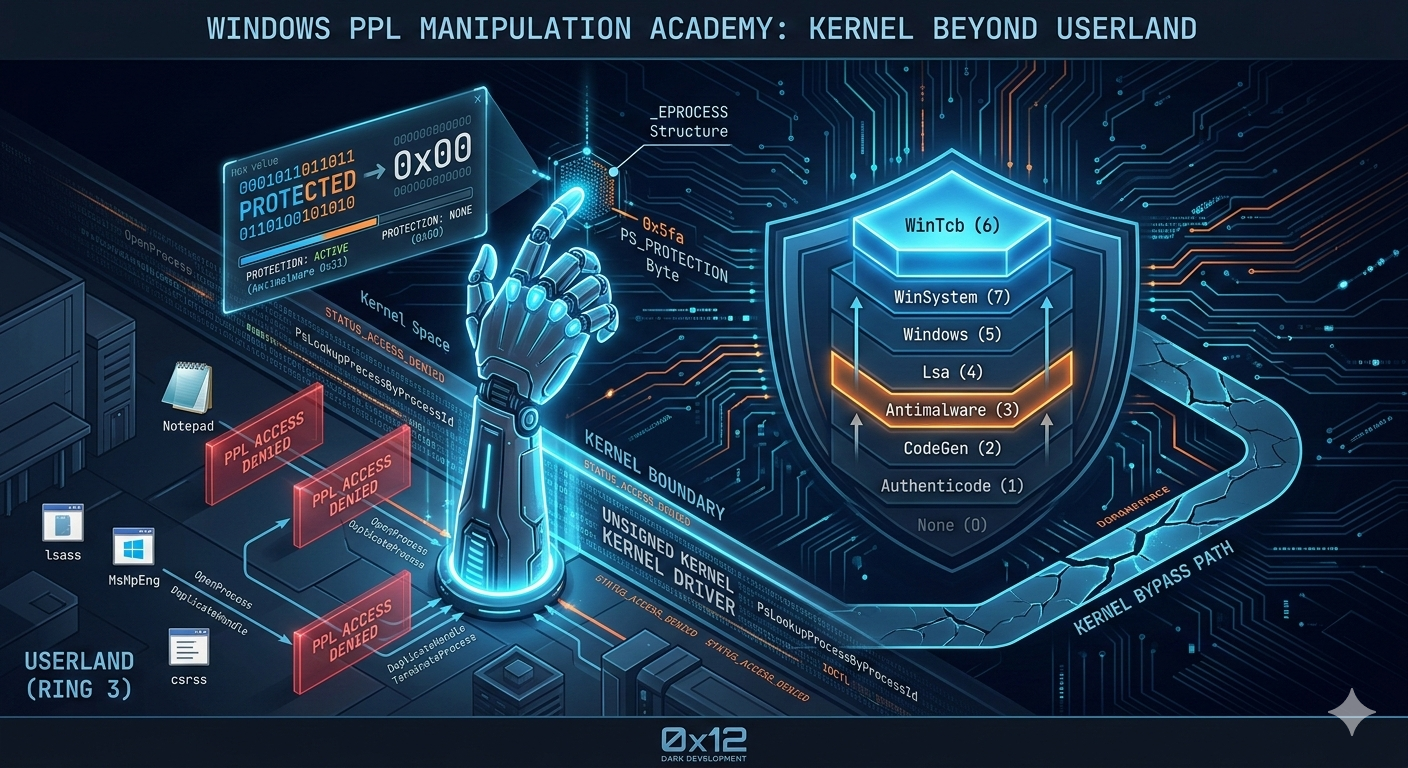
Windows Protected Process Light Part 1
Master Windows Protected Process Light, learn to read, strip, and weaponize kernel-level process trust through direct _EPROCESS manipulation.
|
Evasion | 34 min. | 31 | 08/03/2026 | |

RPC for Malware Development
A hands-on deep dive into Windows RPC as an offensive primitive, from basic IPC to full implant orchestration and EDR evasion.
|
Injection | 43 min. | 38 | 22/02/2026 | |

APC Injection and Shellcode Execution
This module explores advanced process injection techniques using Asynchronous Procedure Calls (APCs), covering everything from classic QueueUserAPC to the stealthy Early Cascade Injection designed to bypass EDR pre-initialization monitoring.
|
Injection | 45 min. | 42 | 09/02/2026 | |

Windows Credential Dumping Techniques
This module covers the evolution of Windows credential dumping techniques, from classic LSASS memory extraction to advanced bypasses of Credential Guard and Remote Credential Guard using protocol abuse and chosen-challenge NTLMv1 attacks.
|
Injection | 32 min. | 34 | 25/01/2026 | |
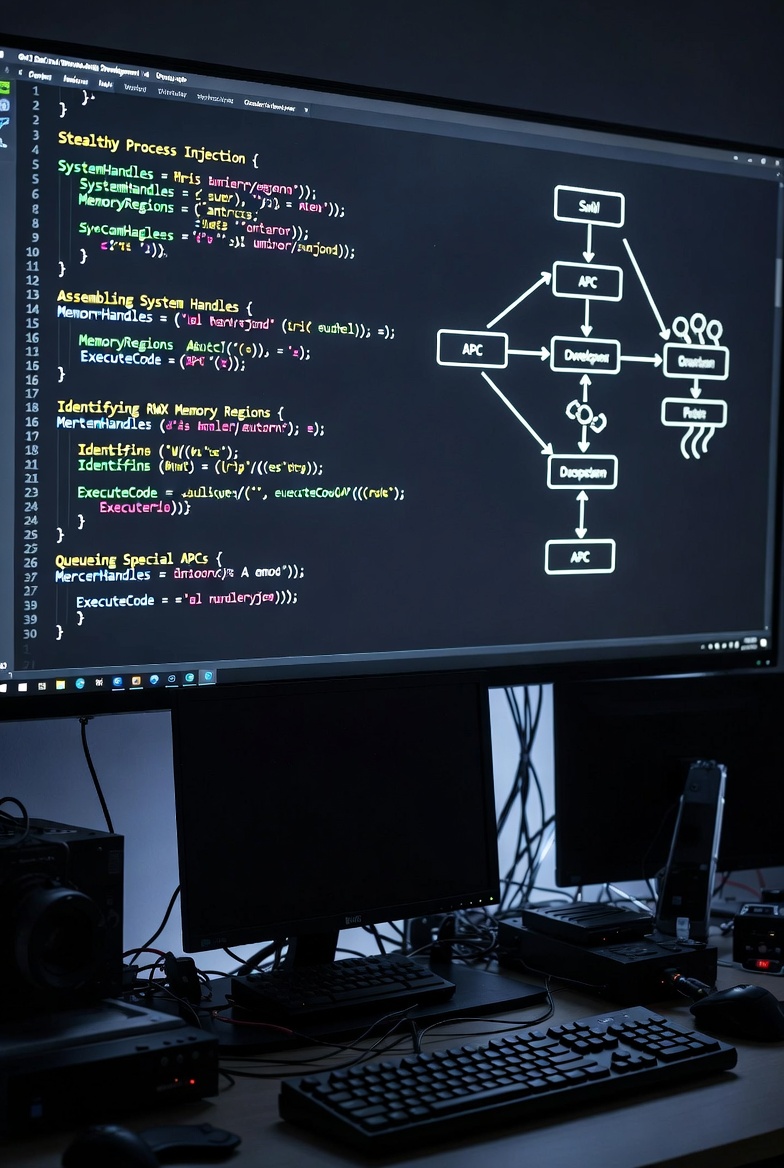
Frankenstein APC Injection
This module covers Frankenstein APC Injection, a novel stealthy process injection technique that reuses existing system handles, RWX memory regions, and special APCs to execute shellcode without triggering common EDR detections.
|
Injection | 35 min. | 39 | 11/01/2026 | |
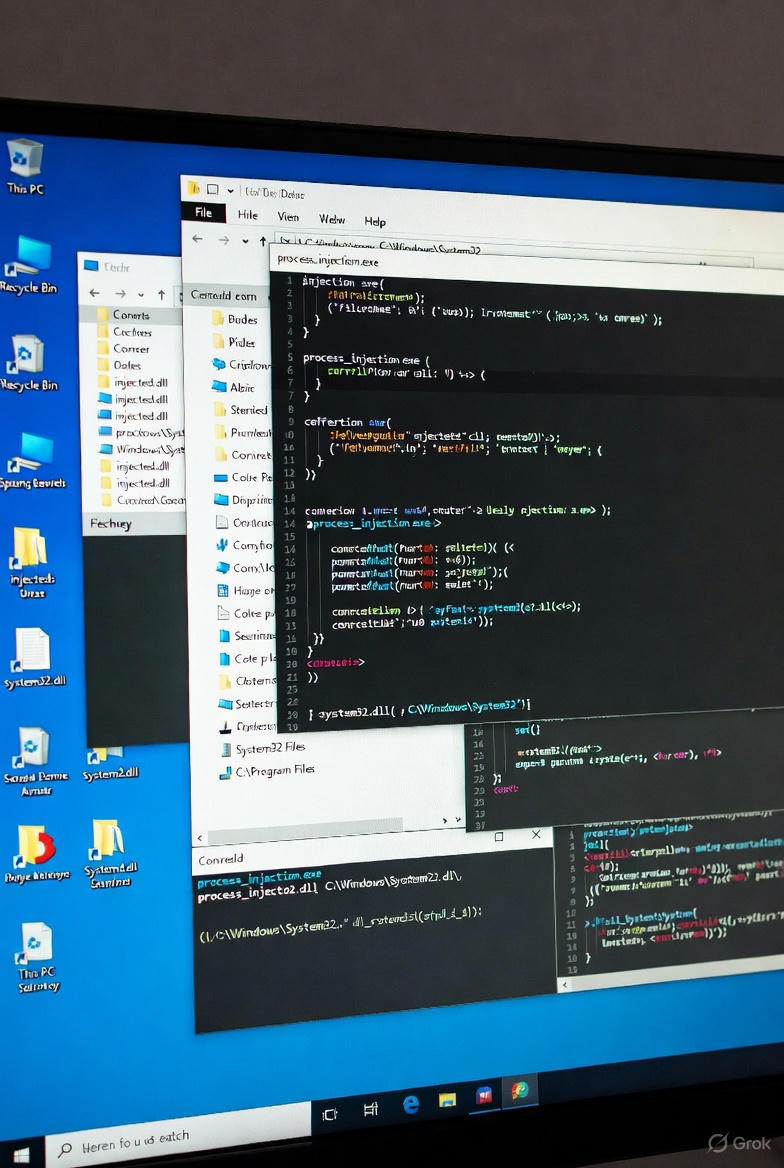
Process Injection Part II
In this second part of the Process Injection we show various interesting techniques like Windows process injection methods including APC-based execution, debugger-assisted hijacking, and memory-mapped migration.
|
Injection | 46 min. | 49 | 14/12/2025 | |

Building Command and Control Server based in Tor Part II
In this second part of the Onion C2 implementation, we have significantly enhanced our command and control infrastructure with enterprise-grade features that transform it from a basic proof-of-concept into robust operational platform.
|
Infrastructure | 49 min. | 51 | 30/11/2025 |